
CIS Controls™ for SaaS – Part 5: Security Awareness and Skills Training
No system is of any use if nobody actually makes use of it. However, the more users your systems have, the more people can inadvertently put your data at risk. This is particularly relevant in the context of SaaS applications which by definition are available globally. So, CIS Control 14 about security awareness training is particularly pertinent.

CIS Controls™ for SaaS – Part 4: Data Protection and Recovery
While you may not be storing the data in your SaaS applications using your own on-premise or cloud infrastructure, keeping the data safe and backed up still remains your responsibility. So, we apply CIS Controls 3 and 11 to a SaaS context to help you do so.

CIS Controls™ for SaaS – Part 3: Secure and Audit
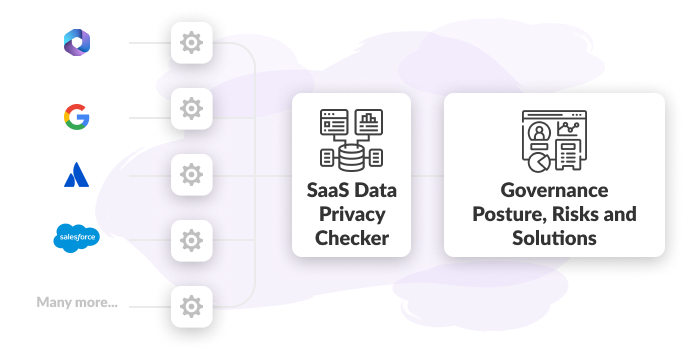
Automated governance is about taking manual, error-prone processes for managing third-party access and replacing them with efficient, repeatable systems. It ensures consistency in policy enforcement, faster identification of risks, and streamlined compliance efforts.

CIS Controls™ for SaaS – Part 2: Account and Access Control Management
One thing that remains almost exclusively your domain in SaaS is account and access management. CIS Controls 5 and 6 make recommendations for this domain and we specifically apply them to SaaS here.

CIS Controls™ for SaaS – Part 1: Inventories
You cannot secure and protect what you do not know you have. Just as the CIS Controls recommend you inventory your enterprise and software assets, it also recommends an inventory for service providers. This is particularly important for SaaS applications which tend to hold a lot of corporate data.

Introduction: What are CIS Critical Security Controls® and Safeguards and how do they apply to Software-as-a-Service (SaaS)?
CIS Critical Security Controls® and Safeguards are general security hygiene recommendations. They were written for a generic context but many can also be applied to achieve good security hygiene in SaaS.
This post is the intro to our series on applying CIS Controls to SaaS.
Automated Governance: Supplier Security
Automated governance is about taking manual, error-prone processes for managing third-party access and replacing them with efficient, repeatable systems. It ensures consistency in policy enforcement, faster identification of risks, and streamlined compliance efforts.
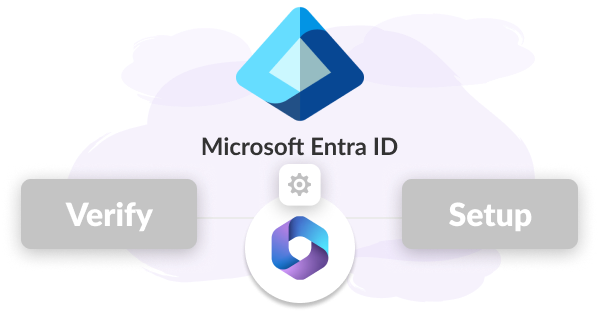
Verifying Your Entra ID MFA and Conditional Access Setup
Transitioning to M365 and Entra ID offers scalability and modern identity management, but ensuring correct configuration is critical to prevent vulnerabilities and compliance gaps.

Non-MS Use Cases: Identifying and removing users from non-Microsoft applications after they leave your company
In the realm of IT management, overseeing user accounts and access to company resources is a fundamental task. While it's common practice to have robust processes for provisioning and de-provisioning users within Microsoft's suite of applications, such as Microsoft 365 (M365), the same diligence often does not extend to non-Microsoft applications.

Tracking changes in user consented applications with Microsoft M365 E3
In today's interconnected digital landscape, user consented applications have become an integral part of our work environments. These applications often enhance productivity and functionality by integrating with platforms like Microsoft 365 (M365).

Identifying, evaluating and tracking user created email forward rules with Microsoft M365 E3
In the digital age, communication flows effortlessly through emails, connecting individuals and businesses across the globe. Microsoft 365 (M365), a comprehensive suite of productivity tools, has revolutionized the way we collaborate.

Discovering and Reporting on DLP Alerts Older than 7 Days with Microsoft M365 E3
As we discussed in the sharing blog, your organization relies on sharing and working with information both internally and externally.Some of that data will be business and customer sensitive. Detexian’s CTO Adrian Kitto has some suggestions about how to get visibility of the DLP alerts beyond the Microsoft Purview defaults of 7 days.

Keeping Abreast of Changes in User Permissions, Configuration, and Access with Microsoft M365 E3
Today Detexian’s CTO Adrian Kitto dives into the risk of privilege creep in M365. He highlights the dangers and the reasons for continuous monitoring which is vital for the modern IT admin to get a handle on changes in user permissions, configuration and access.

Identifying, Evaluating, and Tracking Open Shares for External Users with Microsoft M365 E3
“To share or not to share” is not the question this week, because we all know that your organization relies on sharing and working with information both internally and externally. So this week Detexian’s CTO Adrian Kitto is enabling you to identify and track the risks that external shares in Microsoft M365 are introducing into your organization.

Privileged Access Management in non-SCIM apps with Microsoft M365 E3
Here’s a hard one, how do you track privileged access inside of non-SCIM provisioned applications? Detexian’s CTO Adrian Kitto has a few tips and tricks for you.

Calculating inferred or effective MFA for non-Microsoft applications
Detexian’s CTO Adrian Kitto is delving into a topic that not many will think of; Working out the effective MFA status for non-Microsoft SaaS applications in your organization.

Identifying and removing inactive users with Microsoft M365 E3
Detexian’s CTO Adrian Kitto explores a little understood topic of Inactive Users in M365. These users present security risk and cost wastage so vital for the modern IT admin to get a handle on.

Discovering user consented apps with Microsoft M365 E3
This time Detexian’s CTO Adrian Kitto gets into the nitty gritty of this blog series, tackling discovering user consented applications. He even includes some code samples for you!

How does Microsoft M365 E3 work with the non-Microsoft ecosystem applications?
Detexian’s CTO Adrian Kitto continues with part 2 of his 12 part blog series on tackling some hard productivity and SaaS application security use cases with Microsoft’s M365 E3 product suite.

Why does the mid-market all have Microsoft M365 E3 licenses
Detexian’s CTO Adrian Kitto starts off a 12 part blog series on tackling some hard productivity and SaaS application security use cases with Microsoft’s M365 E3 product suite.
